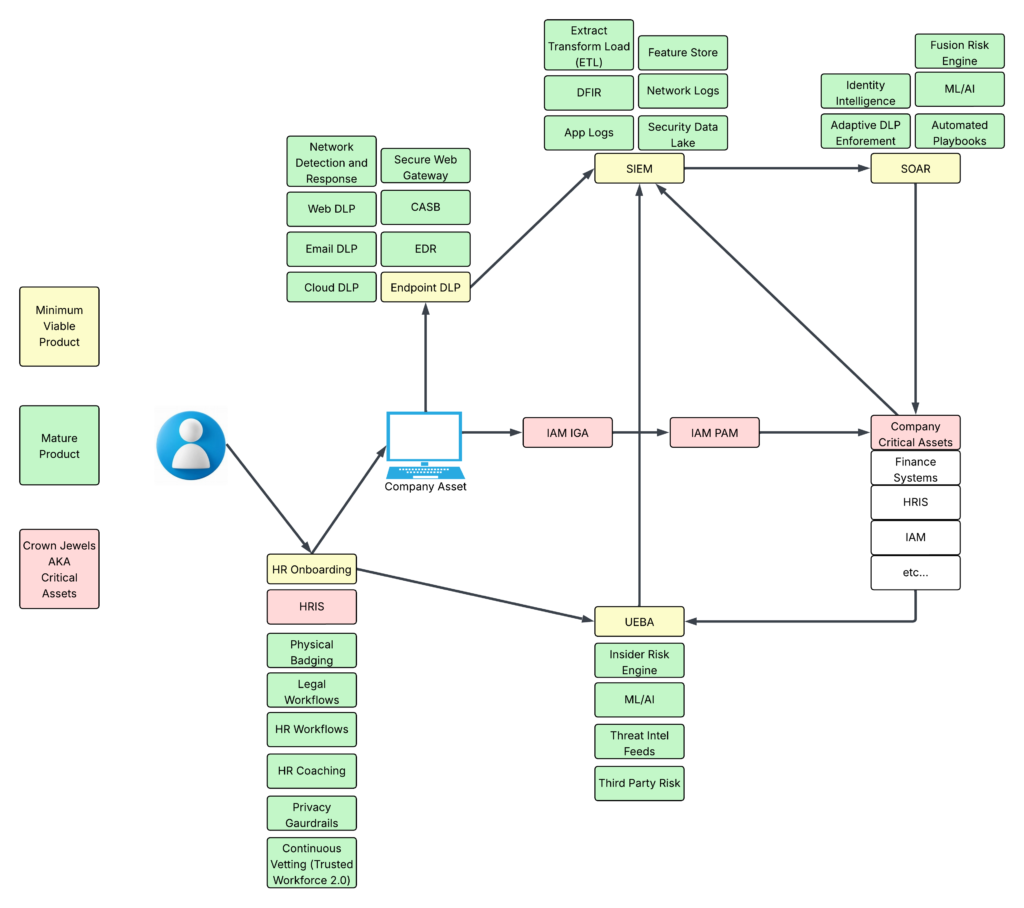
If you want to understand where enterprise security is heading, look at how the pieces connect, not how they operate in isolation. The diagram above captures this shift clearly. Security is no longer a stack of disconnected tools. It is a living ecosystem built around identity, context, and continuous insight.
Everything begins with the user. HR onboarding establishes the earliest signals: who someone is, what they should access, and how their journey starts. That foundation flows into identity governance and privileged access management, which ultimately protect the organization’s most critical assets. But identity alone is only the first layer.
Surrounding it is a dense web of telemetry and intelligence. Network detection, endpoint controls, DLP, and cloud security tools feed massive volumes of data into the SIEM. From there, SOAR and UEBA take over, automating decisions, correlating behaviors, and surfacing subtle risks that humans would never catch in time. Machine learning strengthens these signals, turning raw events into meaningful patterns.
What makes this model powerful is the feedback loop. HR signals influence identity. Identity influences access. Access influences behavior. Behavior influences risk scoring. Risk scoring influences automated enforcement. Every component reinforces the others.
This is the blueprint for a mature security program: not more tools, but more connected tools. Not more alerts, but more context. Not more friction, but smarter, adaptive controls that protect the crown jewels without slowing the business down.
Organizations that embrace this integrated approach will be the ones that thrive. Security becomes dynamic, data-driven, and deeply aware of the humans at its center.