Let’s be honest, the call is often coming from inside the house. While we spend enormous energy building walls to keep external attackers out, the most devastating breaches frequently originate from users we have already trusted and verified.
Preventing insider threats is complex. It’s not just a technical puzzle; it’s a behavioral and cultural challenge that spans human resources, legal counsel, management, and physical security. If you approach it solely with software tools, you will fail.
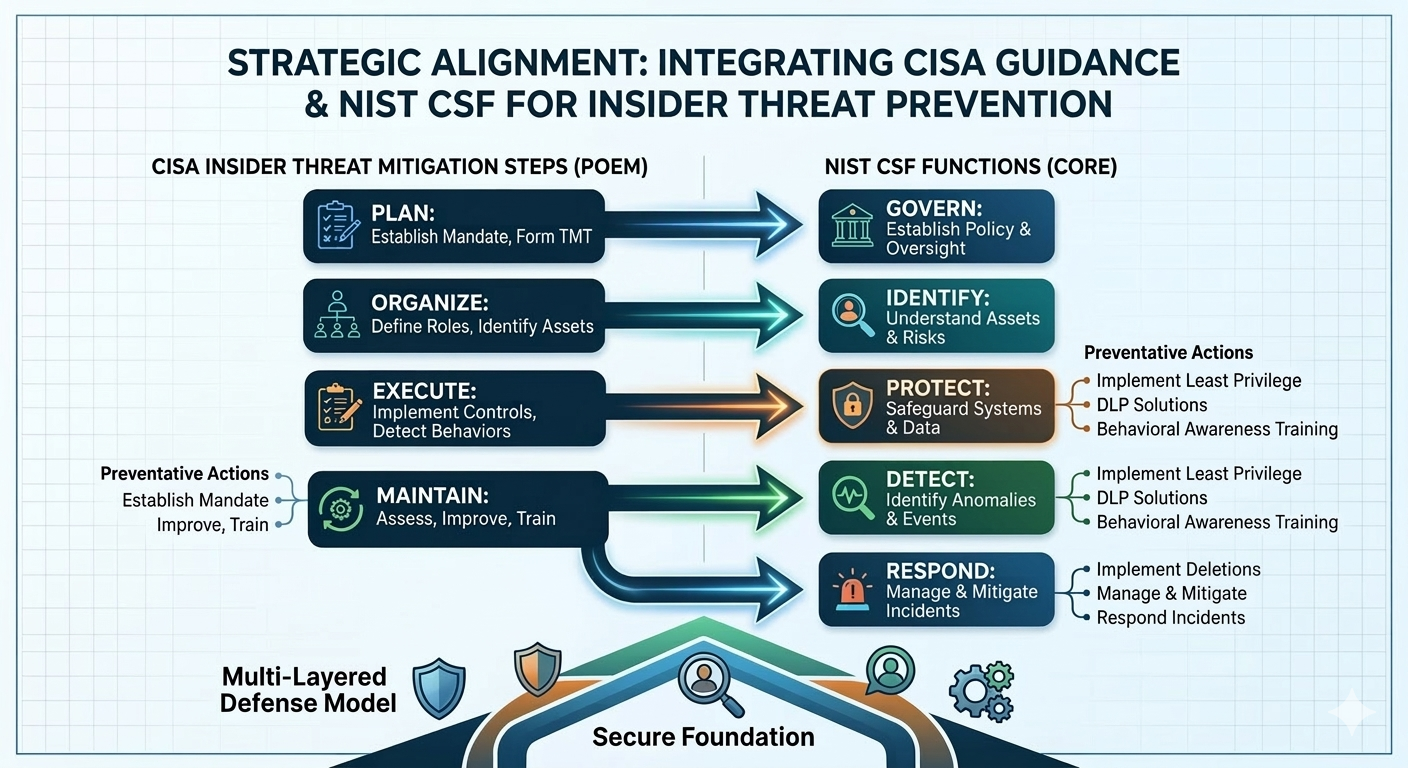
The good news is that you don’t have to reinvent the wheel. We can build a powerhouse strategy by combining two of the most robust, non-proprietary frameworks available: the CISA Insider Threat Mitigation Guide and the NIST Cybersecurity Framework (CSF) 2.0.
By integrating CISA’s specialized “how-to” guidance for insider risk with NIST’s high-level architectural “what-to” outcomes, your organization can move beyond reactive chaos to proactive, defense-in-depth prevention.
The Strategy: Mapping Two Frameworks
Think of NIST CSF as the strategic blueprint for your entire security castle. It tells you that you need strong walls (Protect), reliable lookouts (Detect), and an effective emergency plan (Respond). It provides the structure and goals.
CISA’s Insider Threat Mitigation Guide is your tactical playbook. It tells you exactly how to train those lookouts to recognize a spy (behavioral indicators), how to ensure the trusted guards are still trustworthy, and how the castle administration (HR and Legal) must cooperate to manage the risk.
The most effective approach is to map CISA’s localized, programmatic steps, often summarized as Plan, Organize, Execute, and Maintain (POEM), directly into the five universal Core Functions of the NIST CSF. This ensures that every high-level outcome you want to achieve is fueled by specific, actionable insider threat countermeasures.
1. Governance and Identification: Setting the Rules (NIST: Govern & Identify)
Prevention doesn’t start with firewalls; it starts with policy. You must define the rules of engagement and understand exactly what is at risk. This foundational step must be cross-functional. CISA guidance emphasizes that a dedicated IT project cannot solve an insider threat; it must be a multi-disciplinary program mandated by executive leadership.
How CISA Maps to NIST Govern
- CISA’s “Plan” Phase: Establish the Mandate. This is about high-level buy-in. CISA recommends defining the program’s scope, objectives, and legal/privacy authorities upfront. This aligns perfectly with the Govern (GV) function, ensuring that cybersecurity strategy is integrated with overall enterprise risk management.
- Form the Threat Management Team (TMT). This is a critical CISA action. You must unite HR, Legal, Physical Security, and IT under one banner. This directly satisfies the NIST outcome GV.RR-02: cybersecurity roles and responsibilities are defined and understood.
How CISA Maps to NIST Identify
- Identify High-Value Assets and Critical Functions. Before you can protect anything, you need to know where your “crown jewels” reside. Both CISA and NIST emphasize this asset discovery. However, CISA provides specific context: which assets, if compromised by a trusted user, would have “debilitating effects” on your operation? This critical prioritization feeds into the Identify (ID) function’s risk assessment.
2. Protective Safeguards: Denying Opportunity (NIST: Protect)
This is the point where technical controls merge with behavioral deterrence to actively prevent unauthorized insider actions. The goal is to maximize the friction required for a malicious insider to act, or an accidental insider to make a mistake.
Implement CISA Best Practices via NIST Protect
- Enforce Identity & Access Management (PR.AA). Implement the Principle of Least Privilege. This is foundational. CISA specifically points to high-risk areas like separating user and privileged accounts and, crucially, having a tight, automated process for “revoking credentials for departing employees.”
- Deploy Data-Centric Security (PR.DS). Stop data at the egress point. Both frameworks recommend Data Loss Prevention (DLP) and encryption. But CISA reminds you that your monitoring must respect legal boundaries, especially concerning privacy, so make sure these technical tools are policy-driven.
- Behavioral Awareness & Training (PR.AT). Move beyond “don’t click that phishing link.” CISA urges specialized training to help staff and managers recognize “observable, concerning behaviors.” This might include sudden financial distress, a coworker becoming deeply disgruntled, or attempting to access systems completely outside of their job role.
3. Detection and Analysis: Spotting Anomalies (NIST: Detect)
The most dangerous insiders already have authorized access. Therefore, standard perimeter defenses will not find them. Prevention, in this context, often relies on early detection before a threat can manifest as damage. Your detection strategy must focus on anomalous behavior.
Driving NIST Detection with CISA Tactics
- Technical and Behavioral Monitoring (DE.CM). Implement User and Entity Behavior Analytics (UEBA). While NIST calls for identifying anomalies, CISA’s guidance is key: you need a baseline. UEBA helps technical systems determine what “normal” looks like for a specific user, so it can alert on sudden, unusual spikes in data access or logins at strange hours.
- Establish the Analysis Hub (DE.AE). This is a central recommendation in CISA’s “Execute” phase. You need a way to correlate different signals. System logs showing massive file downloads (technical) are just a signal. They become a high-priority threat when correlated with HR data showing that same employee was just passed over for a promotion or is being actively recruited by a competitor (behavioral indicator). This centralized analysis capability directly enables the Detect (DE) outcomes.
4. Response and Management: Calibrating the Response (NIST: Respond)
Your work isn’t done when a potential threat is identified. Your response must be carefully managed and calibrated based on intent, as well as the technical threat itself. CISA guidance highlights that not all insider threats are malicious; some are accidental or the result of negligence.
Actioning NIST Response with CISA Guidance
- Investigate and Analyze (RS.AN). CISA’s core response step is to “Assess the Threat.” This involves immediate coordination within your TMT (HR, Legal, Security). The TMT must determine if the insider’s actions indicate malicious intent requiring swift legal or physical intervention, or if this is a low-risk scenario that can be handled through re-training.
- Execute Calibrated Mitigation (RS.MI). NIST’s goal is to mitigate the incident. CISA’s nuanced perspective dictates how: a malicious threat might require cooperation with law enforcement and immediate termination, while an accidental breach might result in tightening specific access controls and deploying “just-in-time” training prompts for the affected user.
Preventing insider threats is a continuous loop. The strategic synergy between the NIST CSF and CISA’s programmatic guidance provides the multi-disciplinary structure you need to protect your organization, not just from the outside, but from the trusted inside.
Primary Frameworks
- CISA Insider Threat Mitigation Guide This is the core tactical manual. It details the POEM (Plan, Organize, Execute, Maintain) framework and includes deep dives into forming Threat Management Teams (TMT).
- NIST Cybersecurity Framework (CSF) 2.0 Resource Center The official hub for CSF 2.0. Your readers can download the full framework, access the new “Govern” function details, and find the Small Business Quick Start Guide.
Specialized Implementation Tools
- CISA Insider Threat Mitigation Resources & Tools A curated list of infographics, fact sheets (including HR’s role in prevention), and the Insider Risk Mitigation Program Evaluation (IRMPE) tool.
- CDSE Insider Threat Toolkit An excellent companion resource that provides templates for vigilance campaigns and case studies that help illustrate the “concerning behaviors” mentioned in the post.
- NIST CSF 2.0 Reference Tool An interactive way to explore the Subcategories of the framework, which is helpful for readers looking to map specific technical controls like DLP or UEBA to NIST outcomes.

Leave a Reply