Threat Intelligence
-
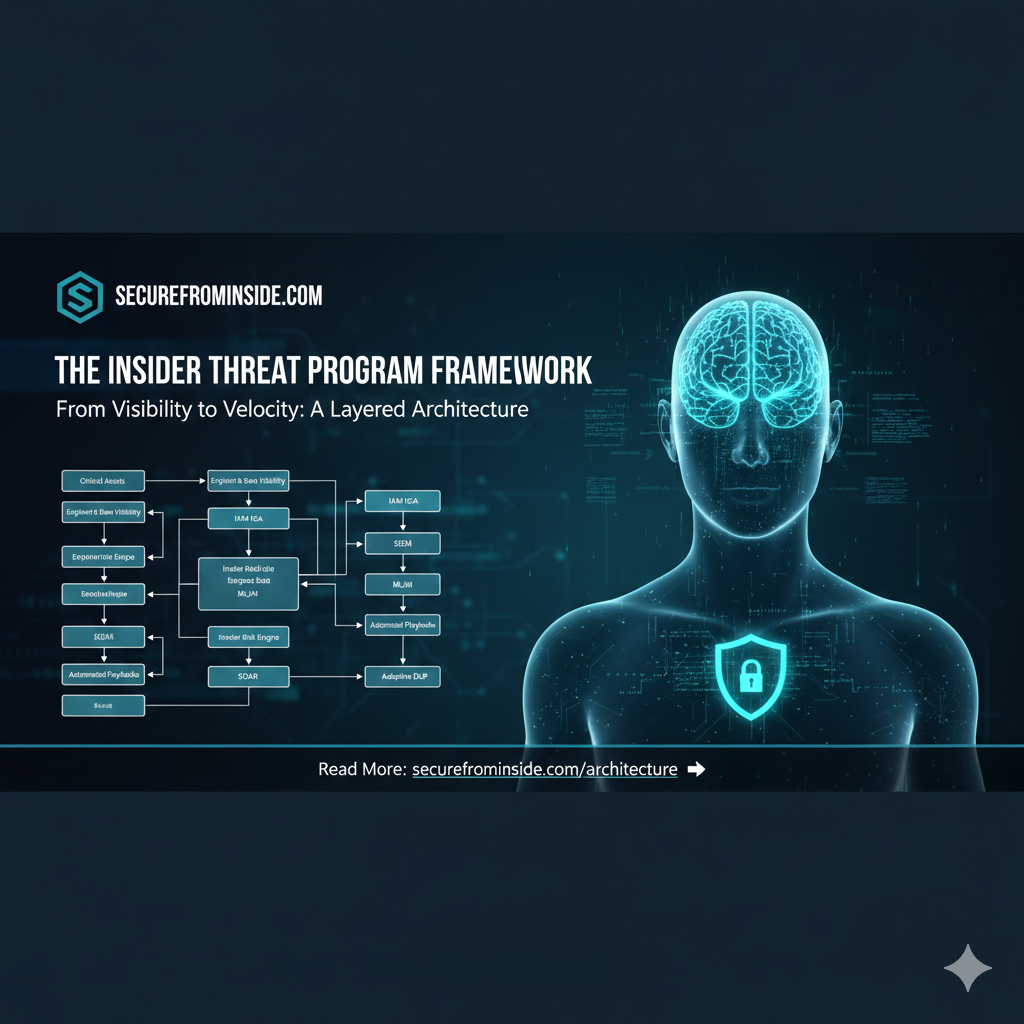
The Modern Security UEBA Blueprint: Where Identity, Behavior, and Automation Converge
If you want to understand where enterprise security is heading, look at how the pieces connect, not how they operate in isolation.…
-

Turning the Tables: How Financial Incentives Can Stop Insider for Hire Attacks
Insider for hire attacks are no longer fringe events. They have become a mainstream tactic for cybercriminals who understand a simple truth.…
-

When Outsiders Act Like Insiders: APT24’s Campaign of Trusted Access
Insider threats are often considered the most dangerous risk in cybersecurity. Employees and contractors already have legitimate access, and when that trust…
-
SilentButDeadly: A Tool That Blocks Security Communications and the Insider Threat Risk
When we talk about endpoint security, most people think of antivirus and endpoint detection and response (EDR) tools as the guardians of…
-

Google’s Emerging Threats Center: Redefining How Security Teams Respond to Cyber Campaigns
Cybersecurity has always been a race against time. When a new vulnerability or attack campaign surfaces, defenders scramble to answer the most…
-
 Advanced Persistent Threat, Artificial Intelligence, Deepfake, Insider Threat, News, Ransomware, Threat Intelligence
Advanced Persistent Threat, Artificial Intelligence, Deepfake, Insider Threat, News, Ransomware, Threat IntelligenceAdversarial Use of AI: What GTIC Found in 2025
Artificial intelligence has officially crossed the threshold from theoretical cybercrime tool to operational reality. According to Google’s Threat Intelligence Group (GTIG), adversaries…
-

The Insider Terrorist Threat: Motivations, Detection, and Prevention
Insider terrorist threats are a serious challenge because they turn trust within organizations into a vulnerability. People with inside access can bypass…
-

Coordinated Insider Threat Activities Across Sectors
Critical infrastructure systems: power grids, water treatment plants, telecommunications, transportation, healthcare, finance, and energy pipelines are the backbone of modern society. As…
-

Why Security Teams Don’t Share Insider Threat Detection Methods
In cybersecurity, openness is usually a strength. Teams share malware signatures, phishing tactics, and attack indicators so that everyone can defend themselves…
-

How Nation States and Consortiums Recruit Insider Threats
Insider threats aren’t just rogue employees; they are often cultivated assets. Nation states and consortiums use calculated strategies to identify, manipulate, and…
Search
Latest Comments
Categories
Archives
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)
