Insider Threat
-

HR Data + AI: The Next Frontier in Insider Threat Detection
Insider threats are uniquely dangerous because they come from trusted employees with legitimate access. Traditional cybersecurity tools catch anomalies in systems, but…
-

What to Do When You Identify an Insider Threat
Insider threats are among the most difficult risks to manage. Unlike external attackers, insiders already have legitimate access, understand internal processes, and…
-

Insider Threats: The Financial Fallout
Insider threats: whether malicious, negligent, or accidental are among the most costly cybersecurity risks. Their financial impact continues to climb, with recent…
-

Using Threat Intelligence to Stop Insider Threats
Insider threats are uniquely dangerous because they exploit legitimate access. Traditional defenses, built to stop external attackers, often miss the subtle signals…
-
Insider Threats in Remote Work Culture: The Unseen Dynamics
Remote work has transformed the modern workplace. It offers flexibility, global collaboration, and resilience regardless of disruptions. But it has transformed the…
-

Zero-Day Exploits and Insider Threats: A Perfect Storm for Cybersecurity
Zero-day exploits are among the most dangerous tools in an attacker’s arsenal. By definition, they target vulnerabilities unknown to vendors and defenders;…
-

AI and Insider Threats: A Double-Edged Sword
Artificial intelligence is rapidly reshaping the cybersecurity landscape. While much of the conversation focuses on AI-driven defense, the reality is more complex:…
-

Post-Quantum Cryptography and Insider Threat: A New Line of Defense
Insider threats have always been one of the most difficult risks to mitigate in cybersecurity. Unlike external adversaries, insiders already have some…
-

Inside the Insider’s Mind: Spotting and Defeating Insider Threats
Insider attacks are stealthy, threatening, and all too easy to underestimate. Get the inside scoop on the most common insider methods –…
-
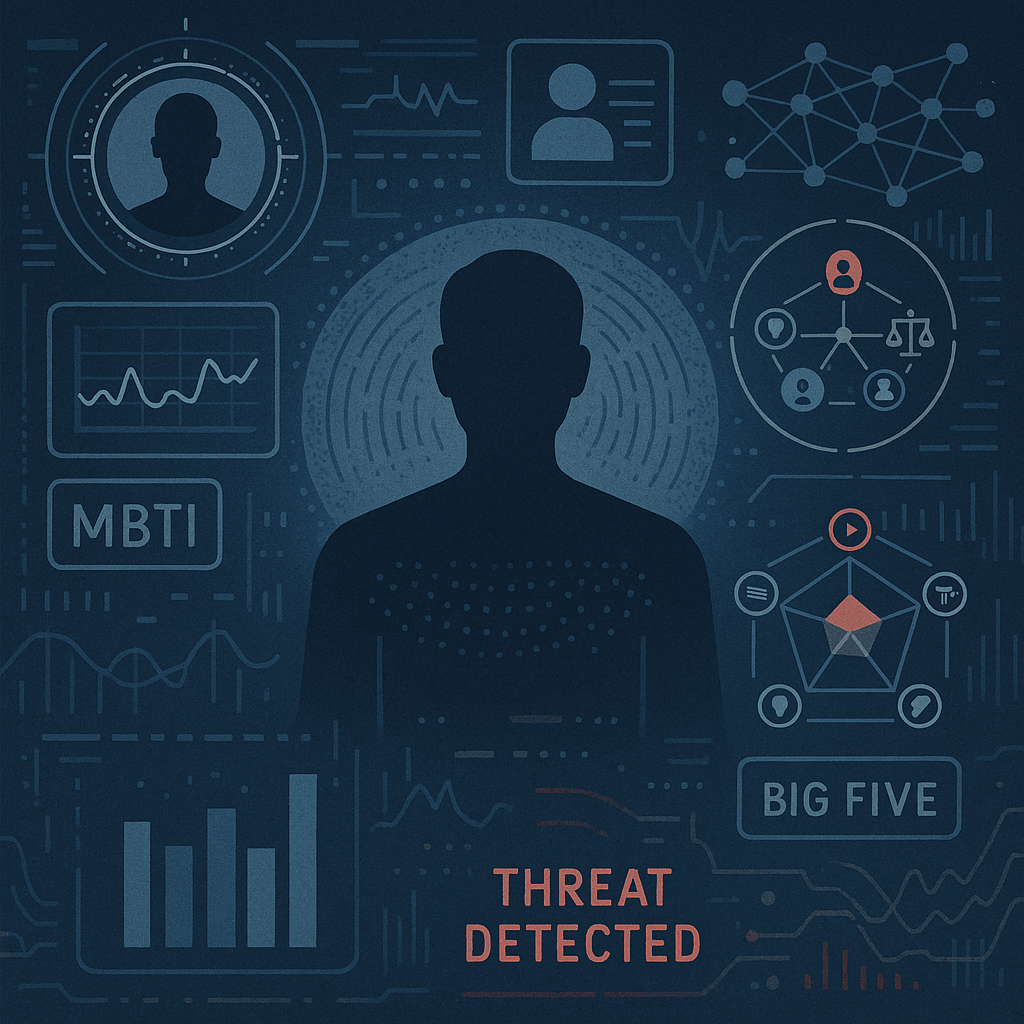
Psychological Profiling and Personality Tests in Insider Threat Detection
When businesses consider insider threats, their minds immediately turn to technical controls – such as access controls, monitoring, and anomaly detection. However,…
Search
Latest Comments
Categories
Archives
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)
