-
The Quiet Reality of Penetration Testing Tools: How Legitimate Tools Become Vectors and What Defenders Must Understand
Insider data theft is one of the most misunderstood risks in modern security programs. When people hear the phrase insider threat, they…
-

The Silent Threat Behind the Monitor: How Hardware Screen Scrapers Are Changing Insider Risk
Most organizations pour enormous resources into defending their digital environments. They deploy endpoint agents, enforce multifactor authentication, monitor logs, and build layered…
-
December 2025: A Rare Month Without Confirmed Insider Breaches, But a Loud Warning About Systemic Insider Risk Conditions
December 2025 will be remembered as an anomaly in an otherwise turbulent year for insider driven security failures. While 2025 saw an…
-
Nvidia’s Insider Threat Case: Lessons From a Trade Secrets Battle
When we talk about cybersecurity, most people picture external attackers hammering away at firewalls or phishing employees to gain access. But some…
-
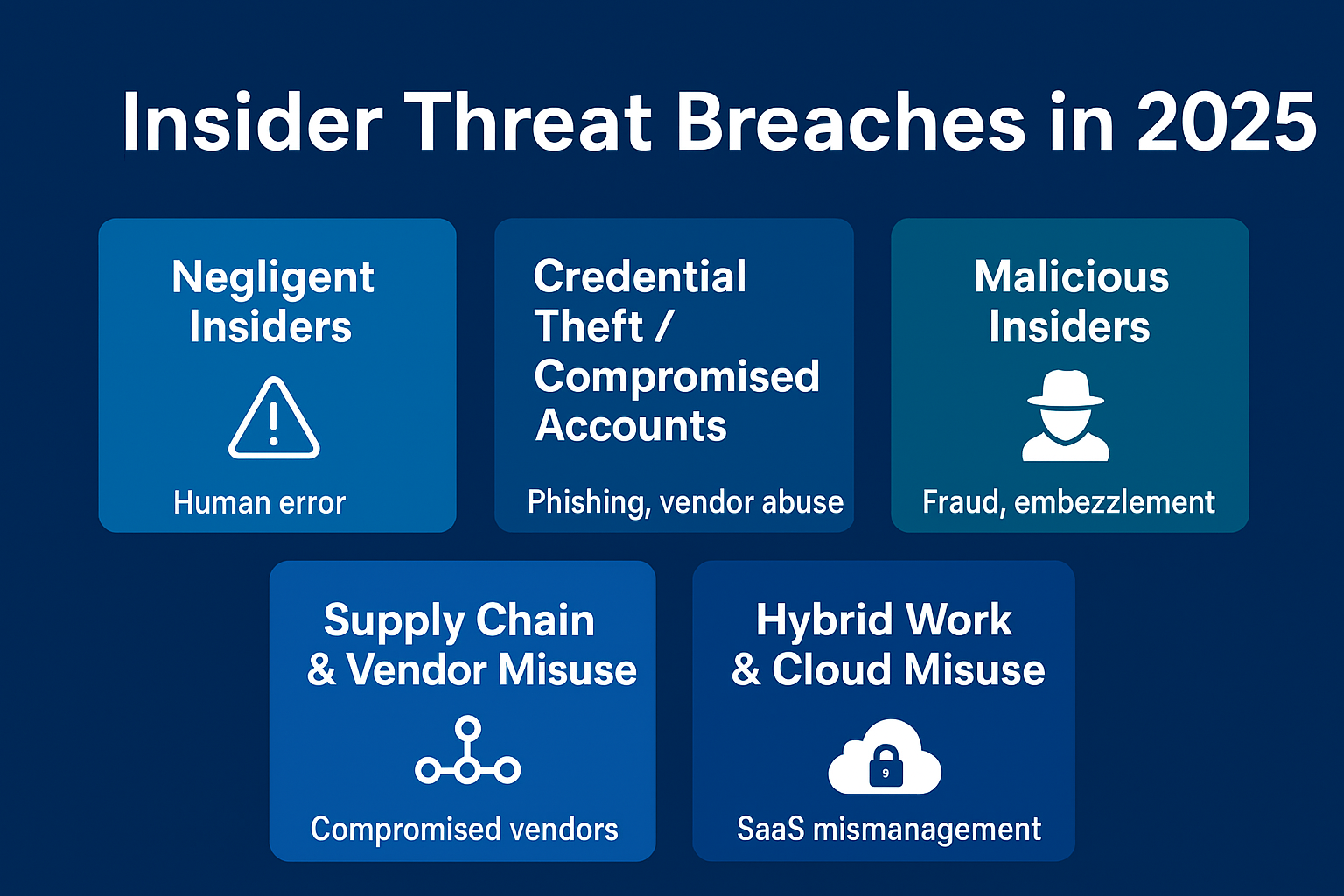
2025 Insider Threat Breach Categories and Examples
Insider threats were one of the most pressing cybersecurity challenges in 2025. Organizations across industries faced breaches caused not only by external…
-

Have You Ever Wondered How Companies Deal With Insider Threats They Do Not Report Externally?
When you read headlines about cyberattacks, the spotlight usually shines on shadowy hackers from outside the organization. What you rarely see are…
-
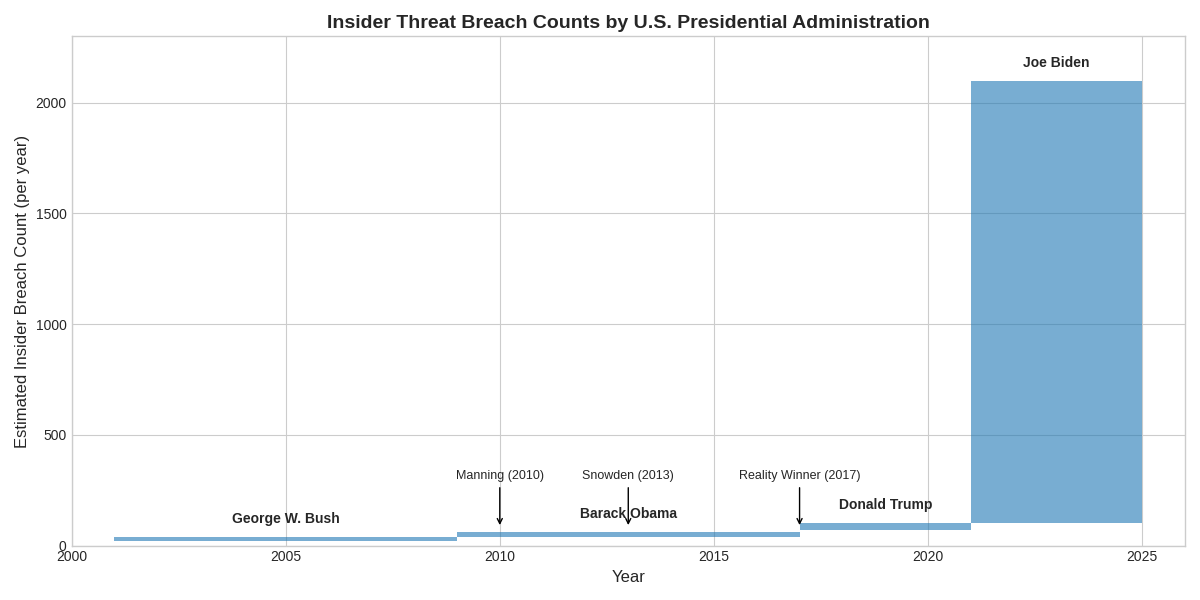
Insider Threat Breaches Across U.S. Presidential Administrations: A Historical Perspective
When we talk about cybersecurity, the spotlight often falls on external adversaries. Nation states, ransomware gangs, and advanced persistent threats dominate headlines.…
-

The Insider Threat Reporting Gap: Silence as the Real Risk
Insider threats are among the most damaging risks organizations face, yet they remain largely invisible in public reporting. While external breaches dominate…
-
Coupang’s Data Breach: A Wake-Up Call on Insider Threats
When news broke in November 2025 that South Korea’s largest e-commerce platform Coupang had suffered a data breach, the initial reports seemed…
-

Global Insider Threats in 2025: Sectoral Deep Dive and Trends
Insider threats surged to record levels in 2025, forcing organizations to rethink cybersecurity and risk management. Whether through negligence, malice, or compromised…
Search
Latest Comments
Categories
Archives
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)
