-

Post-Quantum Cryptography and Insider Threat: A New Line of Defense
Insider threats have always been one of the most difficult risks to mitigate in cybersecurity. Unlike external adversaries, insiders already have some…
-

Inside the Insider’s Mind: Spotting and Defeating Insider Threats
Insider attacks are stealthy, threatening, and all too easy to underestimate. Get the inside scoop on the most common insider methods –…
-
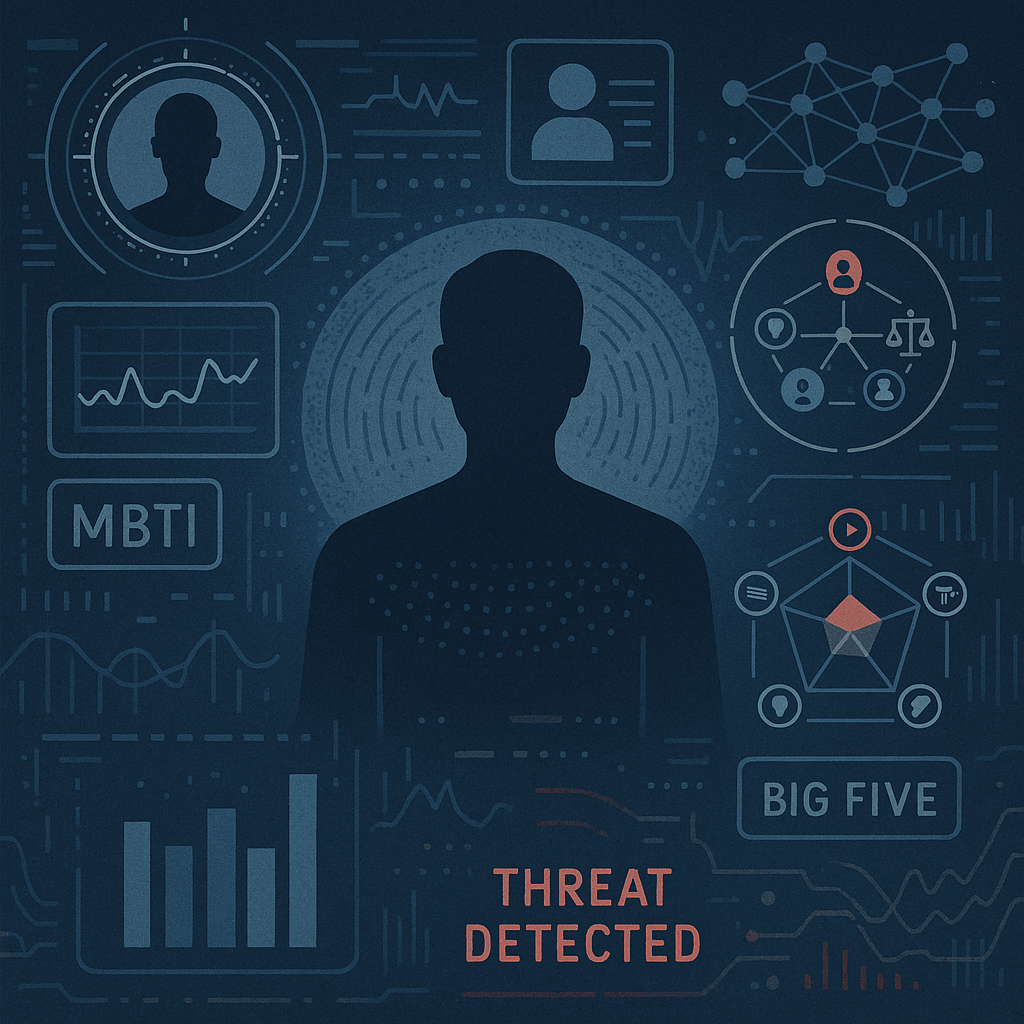
Psychological Profiling and Personality Tests in Insider Threat Detection
When businesses consider insider threats, their minds immediately turn to technical controls – such as access controls, monitoring, and anomaly detection. However,…
-

Social Media Monitoring and Insider Threats: The AI Frontier
Insider threats are challenging to identify because they involve individuals who already have authorized access to data and systems. While tools like…
-

Credit Scores and Insider Threats: A Controversial Perspective on Risk Detection
When organizations consider insider threats, they often focus on technical controls, such as access monitoring, anomaly detection, and privilege management. However, financial…
-

From Trusted Insider to Malicious Threat: Understanding the Transition and Mitigating the Risks
Some of the most significant cybersecurity risks come from within a company. Employees, contractors, or partners who once seemed trustworthy can sometimes…
-

Elevating Cyber Defenses: A Modern Guide to Vulnerability Management for Security Professionals
Introduction: Defining Vulnerability Management in Today’s Threat Landscape In today’s rapidly evolving digital landscape, vulnerability management is essential to any robust cybersecurity…
-

How Insider Threats Begin and How to Stop Them from Escalating Out of Control
Insider threats are usually associated with high-stakes scenarios in popular culture, wherein employees steal trade secrets or contractors breach systems. This’s a…
-

Zero-Day Exploits and Vulnerabilities: A Practical Guide
1. Definition & Context Zero-day exploits are vulnerabilities in software or hardware that are unknown to the vendor and lack an official…
-

Post-Quantum Cryptography: Securing the Future Starts Now
Quantum computing promises breakthroughs in science, medicine, and tech – but also threatens to destroy the cryptographic foundations of our online world.…
Search
Latest Comments
Categories
Archives
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)
