-

The Anthropic Security Crisis: A Masterclass in Negligent Insider Risk
If you had “Major AI Lab accidentally open-sources its proprietary crown jewels” on your 2026 bingo card, congratulations. You’re having a very…
-

The $19.5 Million Blind Spot: March 2026 Insider Threat Roundup
The last 30 days have been a watershed moment for the “insider” definition. New data is showing that the financial stakes have…
-
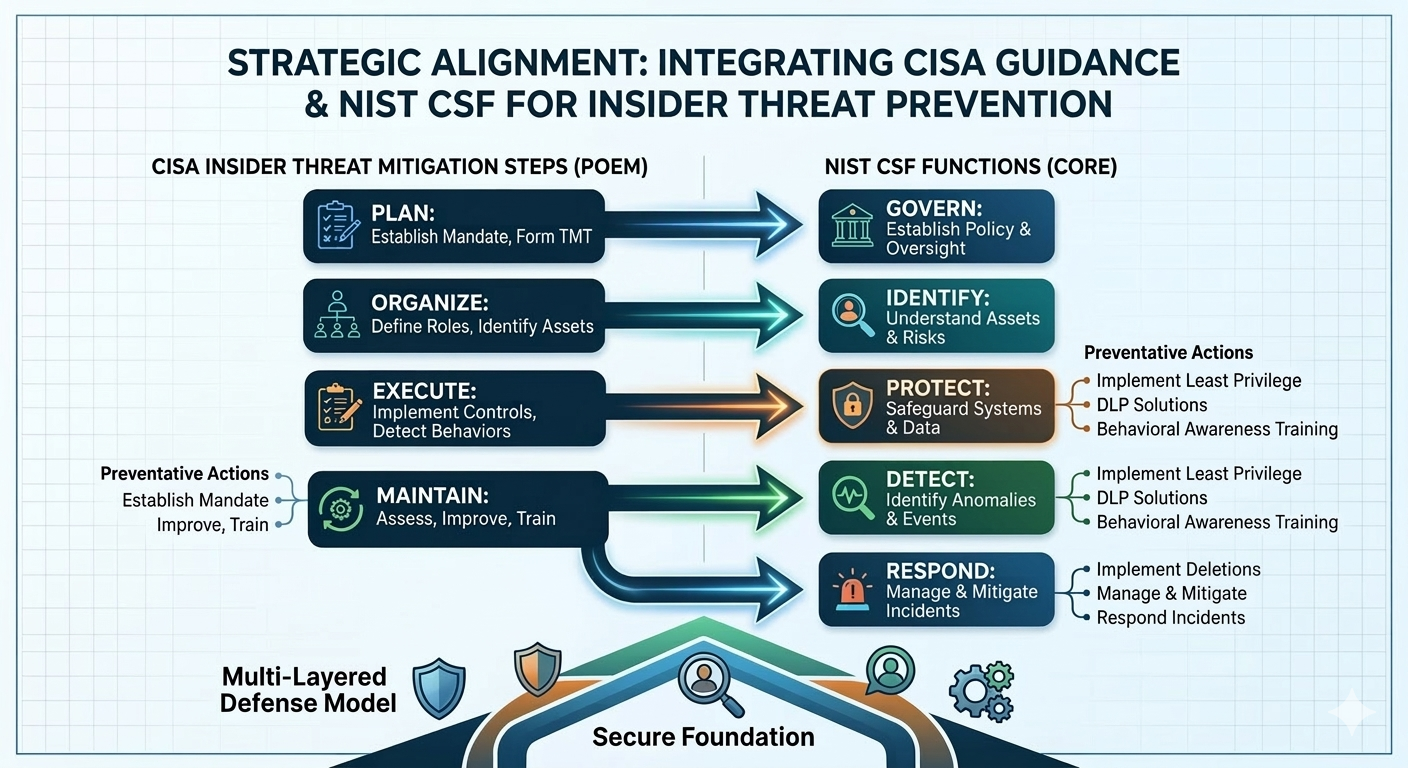
Securing From Inside: A Unified Front Against Insider Threats using CISA Guidance and NIST CSF 2.0
Let’s be honest, the call is often coming from inside the house. While we spend enormous energy building walls to keep external…
-
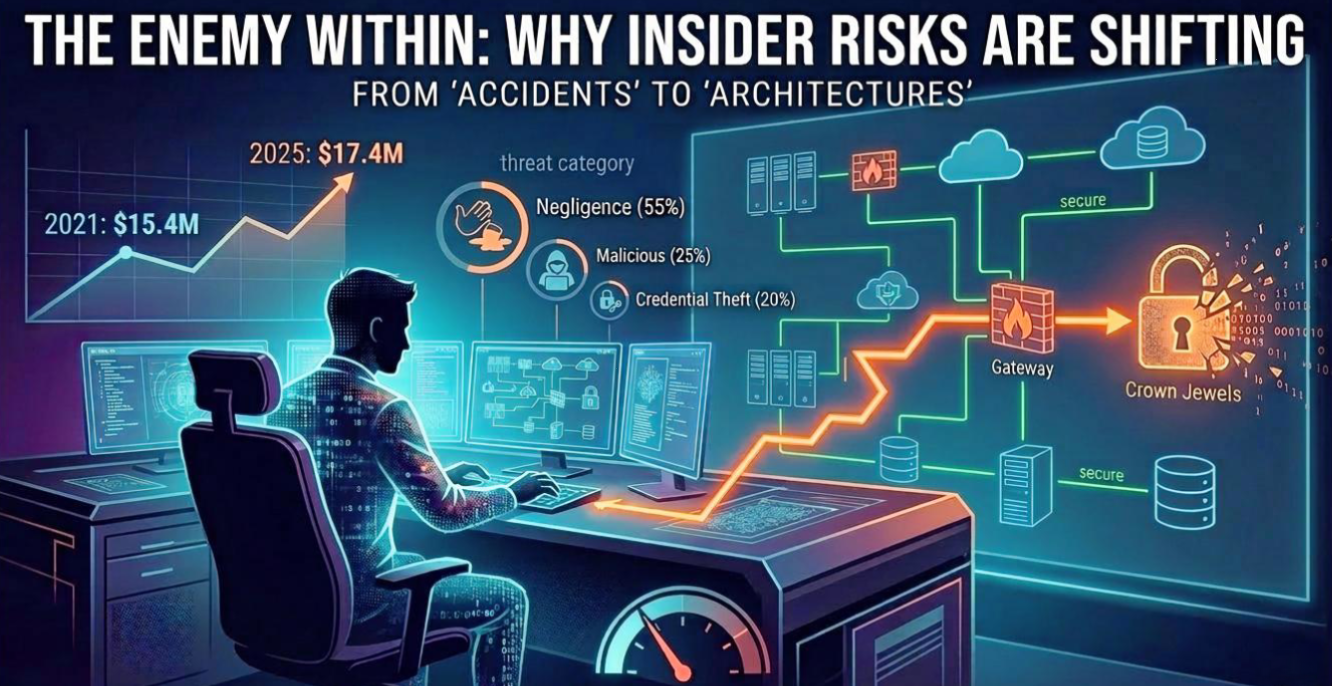
Why Insider Risks are Shifting from “Accidents” to “Architectures”
For years, we treated the “insider threat” as the occasional employee leaving a laptop in a taxi or a disgruntled worker making…
-
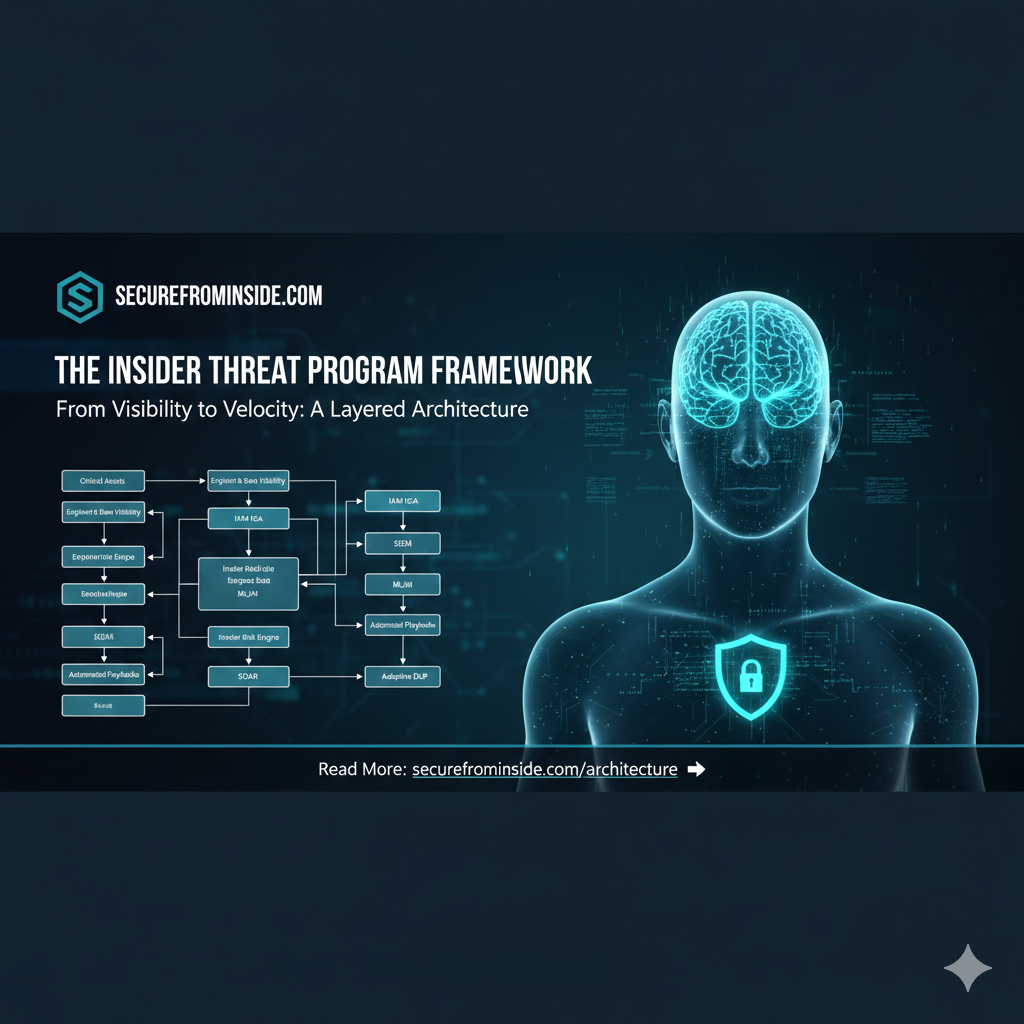
The Modern Security UEBA Blueprint: Where Identity, Behavior, and Automation Converge
If you want to understand where enterprise security is heading, look at how the pieces connect, not how they operate in isolation.…
-
 Contractor (Insider), Data Loss Prevention, HR and HR Flags, Insider Threat, Third Party, User and Entity Behavior Analytics
Contractor (Insider), Data Loss Prevention, HR and HR Flags, Insider Threat, Third Party, User and Entity Behavior AnalyticsThe Enemy Within: Understanding and Mitigating Insider Threats in 2026
The cybersecurity landscape is constantly evolving, and perhaps no threat is more insidious or difficult to detect than the insider. In 2026,…
-

Insider Threats in 2026: A Modern Quick Reference
Insider risk has shifted from a background concern to a defining security challenge. The story is no longer about a rogue employee…
-

Inside the CrowdStrike Insider Incident: How One Employee Exposed a Growing Human Threat and How Financial Incentives Could Have Stopped It
Insider threats rarely arrive with the drama of a ransomware attack or the spectacle of a zero-day exploit. They are quiet. They…
-

The Economics of Trust: How Financial Incentives Reduce Insider Threats
Insider threat is one of the most uncomfortable topics in cybersecurity because it forces us to confront a truth that no one…
-
 Advanced Persistent Threat, Contractor (Insider), Infiltration, Insider Threat, User and Entity Behavior Analytics
Advanced Persistent Threat, Contractor (Insider), Infiltration, Insider Threat, User and Entity Behavior AnalyticsThe New Shape of Insider Threats: Quiet Infiltration, Internal Access Abuse, and the Rise of the Fake Employee
Insider threats are changing again. Not in the dramatic, headline grabbing way that ransomware reshaped the last decade, but in a quieter…
Search
Latest Comments
Categories
Archives
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)
