Recent Articles
-
HR Insider Threats in 2025: The Hidden Risks Inside Your Organization

–
When most people think of insider threats, they picture rogue IT administrators or disgruntled engineers. But in 2025, Human Resources emerged as one of the…
-
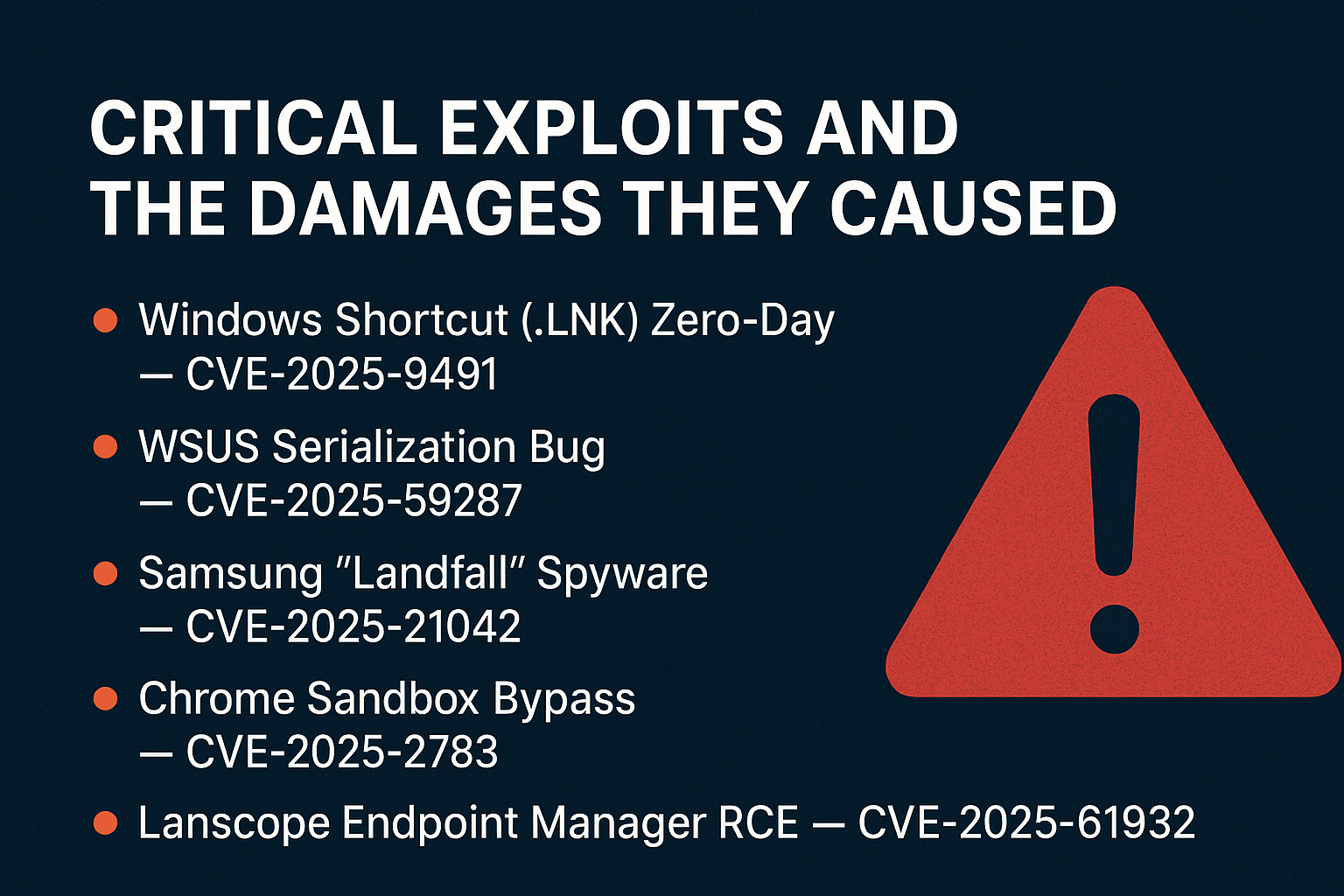
When Zero‑Days Meet Insider Threats: The Real Risk Window

–
Cybersecurity headlines often focus on zero‑day exploits, those mysterious vulnerabilities that attackers discover before vendors even know they exist. But the reality inside most enterprises…
-
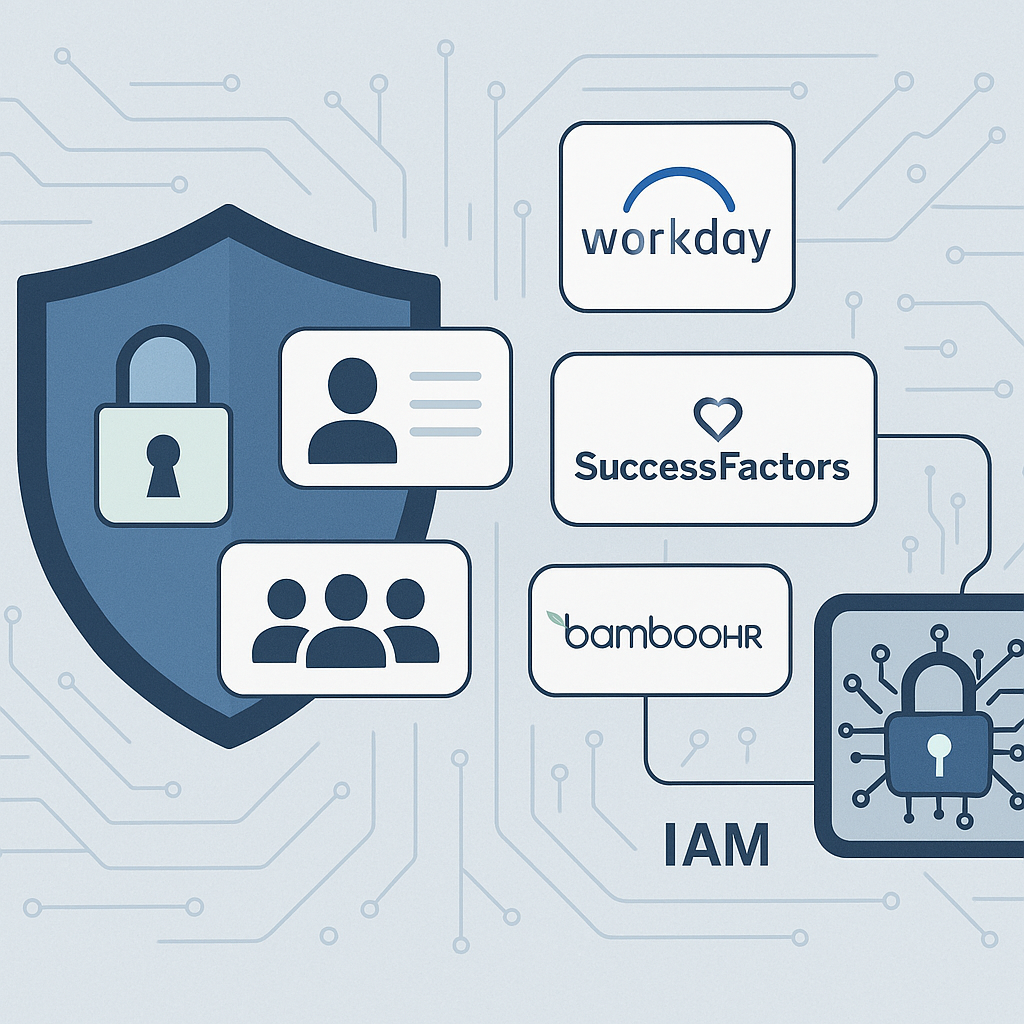
How HR and Cybersecurity Teams Are Joining Forces to Fight Insider Threats

–
In today’s digital workplace, HR systems do more than just manage payroll and benefits. They’re now central to cybersecurity especially when it comes to onboarding,…
-
The Intel Insider Data Theft Incident: Lessons for Enterprise Security

–
In 2024 and 2025, Intel faced one of the most significant insider data theft cases in the technology sector. The breach occurred during a period…
-
Do Companies Really Understand Their Insider Threat Risk Tolerance?

–
When most organizations talk about cybersecurity, the conversation tends to orbit around external attackers: ransomware gangs, nation-state actors, or opportunistic hackers. Yet one of the…
-
The Quantum Insider Threat: What Happens When the Call Comes from Inside the Lab?

–
Quantum computing is one of the most exciting technological frontiers of our time. It promises to revolutionize fields like medicine, logistics, and artificial intelligence. However,…
-
How AI Powered Behavioral Analytics is Transforming Insider Threat Detection

–
Insider threats are among the hardest problems in cybersecurity. Unlike external attackers, insiders already have legitimate access and knowledge of systems, which makes them difficult…
-
Should Employers Retain Psychologists to Deter Insider Threats?

–
Insider threats remain one of the most complex challenges in cybersecurity. While technical defenses can detect anomalies and HR policies can enforce compliance, the human…
-
Psychology and Insider Threats: Reducing the Human Factor

–
Insider threats are one of the most complex challenges in cybersecurity. Firewalls, monitoring tools, and access controls can only go so far when the risk…
-
Insider Threat Red Flags HR Often Misses

–
Insider threats are among the most costly and common risks organizations face. Nearly 60 percent of breaches involve insiders, with average costs in the millions…
-
Artificial Intelligence, Deepfake, Insider Threat, Post Quantum Cryptography, User and Entity Behavior Analytics, Zero Trust
The Future of Insider Threats: Preparing for 2026

–
Insider threats have always been one of the most difficult challenges in cybersecurity. Unlike external attackers, insiders already have legitimate access, context, and trust. Over…
-
UEBA: The Cost-Effective Shield Against Insider Threats

–
Insider threats remain one of the most expensive risks facing enterprises today. According to the Ponemon Institute’s Cost of Insider Threats Global Report 2022, the…
Search
Latest Comments
Categories
Archives
- April 2026 (1)
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)