Recent Articles
-
How Zero Trust Stops Insider Threats: Lessons Across Industries

–
Insider threats, whether from malicious employees or compromised accounts, are among the most dangerous cybersecurity risks today. Traditional perimeter-based security models often fall short, assuming…
-
Spotting Insider Threats: What Leaders and Employees Should Watch For

–
Insider threats, risks that come from within an organization, are among the hardest to detect and most damaging. Whether intentional or accidental, these threats often…
-
HR Data + AI: The Next Frontier in Insider Threat Detection

–
Insider threats are uniquely dangerous because they come from trusted employees with legitimate access. Traditional cybersecurity tools catch anomalies in systems, but they often miss…
-
What to Do When You Identify an Insider Threat

–
Insider threats are among the most difficult risks to manage. Unlike external attackers, insiders already have legitimate access, understand internal processes, and can bypass many…
-
Insider Threats: The Financial Fallout

–
Insider threats: whether malicious, negligent, or accidental are among the most costly cybersecurity risks. Their financial impact continues to climb, with recent data showing staggering…
-
Using Threat Intelligence to Stop Insider Threats

–
Insider threats are uniquely dangerous because they exploit legitimate access. Traditional defenses, built to stop external attackers, often miss the subtle signals of an insider…
-
Insider Threats in Remote Work Culture: The Unseen Dynamics

–
Remote work has transformed the modern workplace. It offers flexibility, global collaboration, and resilience regardless of disruptions. But it has transformed the insider threat landscape…
-
Zero-Day Exploits and Insider Threats: A Perfect Storm for Cybersecurity

–
Zero-day exploits are among the most dangerous tools in an attacker’s arsenal. By definition, they target vulnerabilities unknown to vendors and defenders; meaning patches don’t…
-
AI and Insider Threats: A Double-Edged Sword

–
Artificial intelligence is rapidly reshaping the cybersecurity landscape. While much of the conversation focuses on AI-driven defense, the reality is more complex: AI is a…
-
Post-Quantum Cryptography and Insider Threat: A New Line of Defense

–
Insider threats have always been one of the most difficult risks to mitigate in cybersecurity. Unlike external adversaries, insiders already have some level of trust,…
-
Inside the Insider’s Mind: Spotting and Defeating Insider Threats

–
Insider attacks are stealthy, threatening, and all too easy to underestimate. Get the inside scoop on the most common insider methods – from privilege abuse…
-
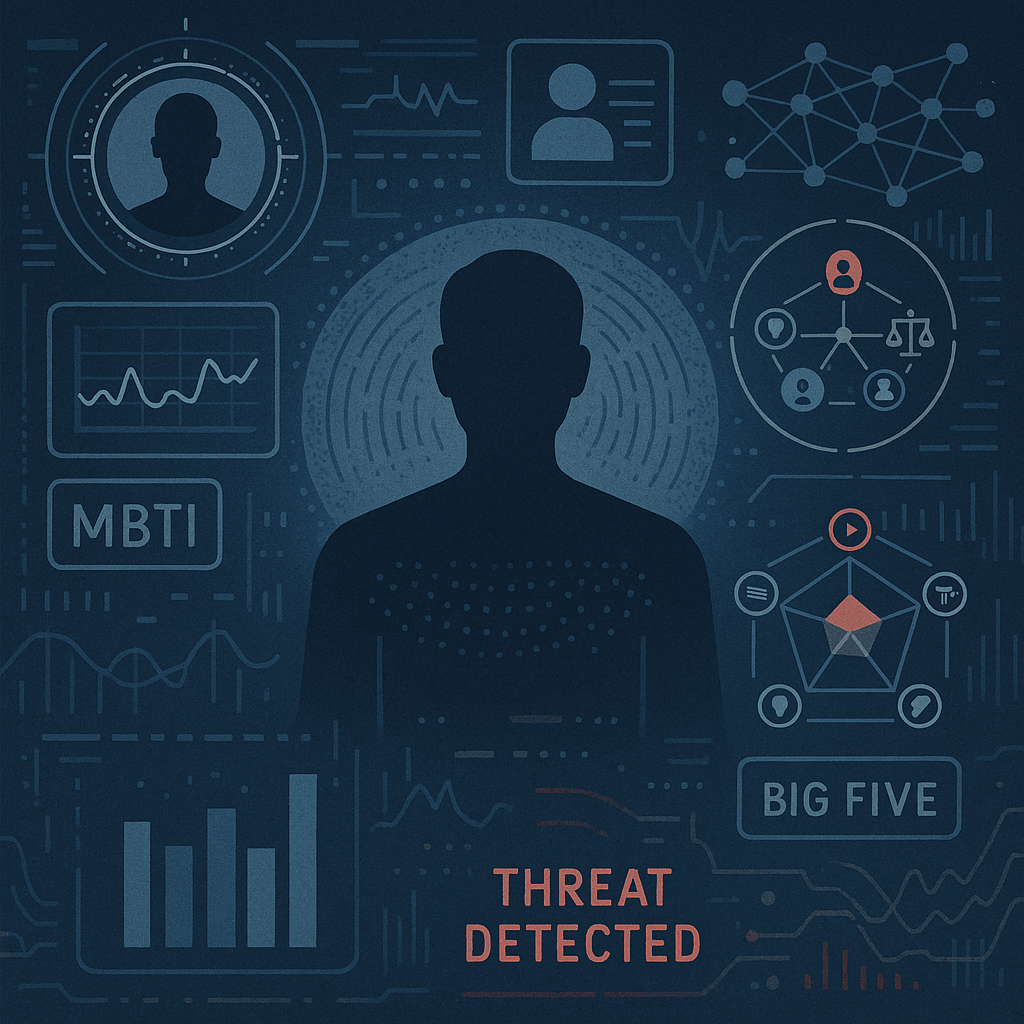
Psychological Profiling and Personality Tests in Insider Threat Detection

–
When businesses consider insider threats, their minds immediately turn to technical controls – such as access controls, monitoring, and anomaly detection. However, a second aspect…
Search
Latest Comments
Categories
Archives
- April 2026 (1)
- March 2026 (4)
- February 2026 (9)
- January 2026 (3)
- December 2025 (19)
- November 2025 (73)
- October 2025 (45)